Ensuring the Security of Your Business in a Digital World
In today’s hyperconnected world, cybersecurity has become an increasingly pressing concern for businesses of all sizes. As technology advances at an unprecedented rate, so do the threats that come with it. Cybercriminals constantly evolve tactics, looking for vulnerabilities to exploit and sensitive information to steal. With October being National Cybersecurity Awareness Month, there’s no better time to dive into the topic and equip your business with the knowledge needed to protect itself from online threats.
The Growing Importance of Cybersecurity Awareness Month
The Rising Threat Landscape for Businesses
Cyber attacks have become more frequent and sophisticated in recent years, posing a significant threat to businesses across all industries. No business is immune to these risks, from small startups to multinational corporations. Hackers target vulnerabilities in systems, networks, and employees’ behaviors, attempting to gain unauthorized access to valuable data or disrupt critical operations. Without adequate cybersecurity measures in place, businesses are left exposed and vulnerable.
If you’re worried your business is vulnerable, check out Small Business Vulnerability: 5 Top Ways Continuous IT Monitoring Keeps You Safe.
The High Costs of Cyber Attacks: A Real-World Perspective
The financial impact of a cyber attack can devastate businesses. Long-term consequences can significantly affect an organization’s bottom line beyond the immediate costs of incident response and remediation. Lost revenue, damaged brand reputation, legal fees, regulatory fines, and potential lawsuits are just a few examples of the fallout from a successful cyber attack. According to recent studies, the average data breach cost has reached staggering amounts ($4.45 million in 2023), demonstrating the importance of proactive measures even more than celebrating National Cybersecurity Awareness Month.
Building a Culture of Cybersecurity: The Role of Employee Education
While technology is crucial in protecting your business from cyber threats, fostering a culture of awareness among your employees is equally important. This Cybersecurity Awareness Month, why not take the opportunity to incorporate continuing education into your business environment?
Human error is one of the leading causes of security breaches, making employee education a vital component of any comprehensive cybersecurity strategy. By providing regular training sessions, promoting best practices, and creating an open dialogue about cybersecurity, you empower your workforce to become your first line of defense against cybercriminals.
Essential Steps to Strengthen Your Business’s Cyber Defenses
Conducting a Comprehensive Risk Assessment
To safeguard your business against cyber threats effectively, it’s a good idea to start by conducting a thorough risk assessment. This process involves identifying and evaluating the potential vulnerabilities within your organization’s systems, networks, and operations. Understanding where your weaknesses lie allows you to prioritize your efforts and allocate resources more effectively. Total Computer Solutions can help you perform an in-depth analysis and provide recommendations tailored to your needs.
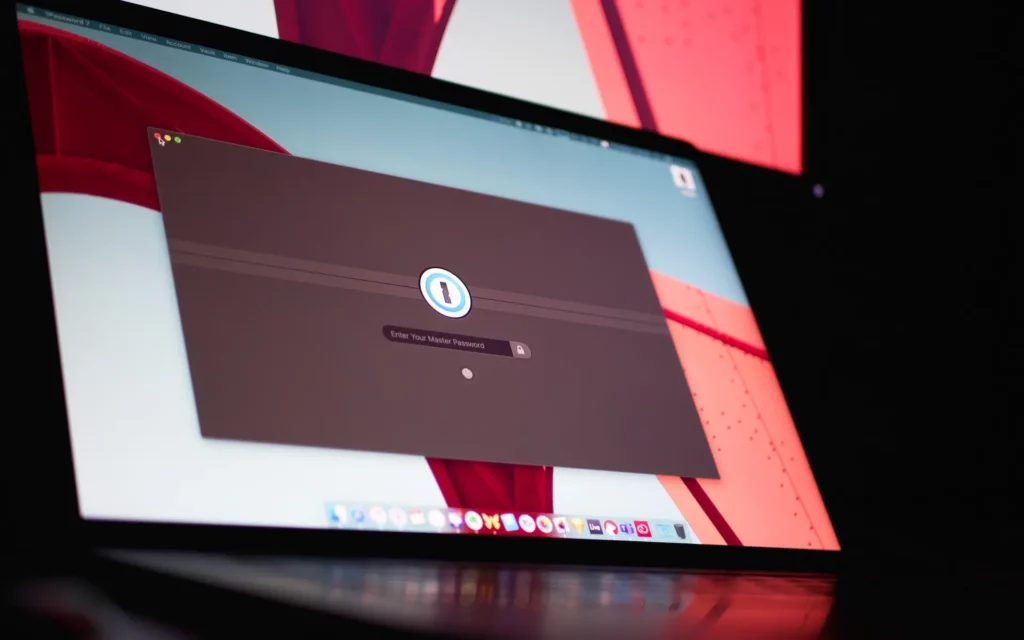
Implementing Robust Password Practices
Passwords remain one of the most critical lines of defense against unauthorized access. Unfortunately, weak passwords are still prevalent and easily exploited by cybercriminals. To strengthen your business’s defenses, encourage employees to create strong, unique passwords that combine upper and lowercase letters, numbers, and special characters. Implementing multi-factor authentication (MFA) adds an extra layer of security by requiring users to verify their identity through additional means, such as biometrics or a secondary device.
Keeping Systems and Software Up to Date
Outdated systems and software pose significant risks to your business’s cybersecurity. Cybercriminals often target known vulnerabilities in outdated technology, which may have patches or updates available to address those weaknesses. Regularly updating your systems and software ensures you have the latest security features and reduces the chances of falling victim to opportunistic attacks. Establish a system for monitoring and applying updates promptly to minimize your exposure to threats.
Navigating the Complexities of Network Security
Securing Your Wireless Networks: Best Practices
Wireless networks play a crucial role in modern businesses, enabling seamless connectivity and productivity. However, they can also be a weak link if not adequately secured. Start by changing default login credentials on routers and access points to prevent unauthorized access. Implement Wi-Fi Protected Access (WPA2) or newer protocols to encrypt data transmissions. Segregate guest networks from internal networks to minimize potential risks. Regularly review access logs and monitor network traffic for any signs of suspicious activity.
Implementing Firewalls and Intrusion Detection Systems
Firewalls act as a barrier between your internal network and external threats, filtering incoming and outgoing traffic based on predetermined security rules. They play a critical role in preventing unauthorized access to your systems and can be configured to monitor and block specific types of traffic. Combining firewalls with intrusion detection systems (IDS) provides an added layer of protection by detecting and alerting you to potential intrusions or suspicious activities within your network.
Encrypting Sensitive Data: An Extra Layer of Protection
Data encryption is essential for protecting sensitive information from unauthorized access. By converting data into an unreadable format that can only be deciphered with the correct encryption key, even if intercepted, it remains useless to cybercriminals. Prioritize encrypting data at rest (stored on servers or devices) and data in transit (transmitted across networks). Additionally, consider utilizing virtual private networks (VPNs) to create secure tunnels for remote workers accessing your business’s resources.
The Power of Cloud Computing in Cybersecurity
Cloud computing has revolutionized how businesses store and access their data. With its many benefits, including scalability, cost-effectiveness, and ease of collaboration, cloud storage has become an indispensable tool for organizations of all sizes. However, it’s important to understand the associated risks and take appropriate measures to safeguard your data. Partnering with a trusted cloud service provider that prioritizes robust security practices and offers comprehensive backup and disaster recovery solutions should be a top priority.
Selecting a Trusted Cloud Service Provider
When choosing a cloud service provider, conducting due diligence is crucial. Look for providers with stringent security protocols, adhere to industry best practices, and maintain high transparency regarding their infrastructure and data handling processes. Consider factors such as data encryption capabilities, data sovereignty options, compliance with regulatory requirements, and their track record for incident response and customer support. Selecting the right partner will give you peace of mind that your data is safe.
TCS can help you store and maintain your data on a secure cloud network managed by our IT professionals.
Backing Up Data: Preventing Disastrous Losses
No cybersecurity strategy is complete without robust data backup practices. In a cyber-attack or system failure, readily available recent backups can differentiate between minimal disruption and potentially catastrophic losses. Implement regular backup schedules, verify the integrity of your backups through periodic testing, and store them securely on-premises and off-site. Following this practice ensures business continuity and expedites recovery efforts should the worst happen.
The Crucial Role of IT Consulting in Maintaining Cyber Resilience

Partnering with Experts: Unlocking the Full Potential of Technology
Navigating the complex cybersecurity landscape requires expertise and up-to-date knowledge. This is where IT consulting comes into play. Engaging TCS’s experienced cybersecurity professionals allows you to leverage their skills, experience, and industry insights to maximize your organization’s defenses. We can provide strategic guidance, help design and implement security solutions tailored to your needs, and assist with ongoing monitoring and proactive threat detection.
Developing Incident Response Plans
Preparation is key when it comes to mitigating the impact of a cybersecurity incident. Having well-defined incident response plans ensures that your team knows how to respond swiftly and effectively in the event of an attack. These plans outline step-by-step procedures for identifying, containing, eradicating, and recovering from cyber threats while minimizing damage and downtime. Regularly test and update these plans as new risks emerge and technology evolves.
Training Employees: The First Line of Defense
Employees are often the weakest link in the cybersecurity chain, but they also have the potential to be your strongest asset. Investing in employee training programs that recognize phishing attempts, practice good password hygiene, understand social engineering tactics, and follow security protocols can significantly enhance your organization’s resilience. Regularly communicate updates, reinforce best practices, and foster a culture of accountability to ensure that Cybersecurity Awareness Month remains top of mind for all employees every month.
ProTip: Try some of the below training ideas to ensure your employees stay up-to-date this cybersecurity awareness month.
- Host a lunch and learn. Invite employees to attend a company-sponsored event that provides them with food and education at the same time. Your lunch and learn event could cover the basics of cybersecurity, how to recognize phishing attempts, and more. Check out TCS’s free guides for training resources.
- Provide a challenge. Consider providing a challenge that will encourage employees to test their cyber security skills or reward the person who prevents a “threat” from slipping through. Conduct a mock penetration by sending a phishing email or calling your employees, then see who passes. Those who pass the challenge win a prize!
- Design a survey. What do your employees already know about cybersecurity? Do they feel that their skills are lacking in this area? More importantly, are their skills as strong as they believe they are? Survey of your employees. Ask them to rate their cyber security skills or to answer basic questions about security–or both! Your survey will give you a better idea of what your employees already know, allowing you to focus future educational efforts on the areas where they might be weaker.
- Consider the benefits of TCS Cyber Sheild. TCS CyberShield provides your business with a fully functional cybersecurity partner. It delivers peace of mind with industry-leading security practices and best-in-class tools.
Empowering Your Business Through Preparedness This Cybersecurity Awareness Month
As technology advances rapidly, the importance of cybersecurity cannot be overstated. Safeguarding your business from online threats requires a multifaceted approach that combines robust technological solutions, ongoing employee education, and strategic partnerships with IT consultants. By implementing essential cybersecurity measures such as conducting risk assessments, strengthening password practices, staying updated on system patches, securing wireless networks, leveraging cloud storage securely, and investing in employee training, you can build a strong defense against cybercriminals.
Cybersecurity Checklist
If you’re still unsure how protected your business is, review how it holds up to TCS’s cybersecurity checklist below.
- Conduct a comprehensive risk assessment to identify vulnerabilities within your organization.
- Implement strong password practices and consider multi-factor authentication for added security.
- Keep systems and software up to date to prevent opportunistic attacks.
- Secure wireless networks by changing default login credentials, using encryption protocols, and monitoring network activity.
- Utilize firewalls and intrusion detection systems to detect and prevent unauthorized access.
- Encrypt sensitive data at rest and in transit to protect it from unauthorized access.
- Choose a trusted cloud service provider that prioritizes security and offers comprehensive backup solutions.
- Establish regular backup schedules and verify the integrity of backups through periodic testing.
- Partner with IT consultants to leverage their expertise and maximize your cybersecurity defenses.
- Develop incident response plans to mitigate the impact of cyber threats.
- Invest in employee training programs to foster a culture of cybersecurity awareness and accountability.
Taking proactive steps to protect your business from cyber threats is essential and crucial in today’s digital landscape. By implementing the strategies and best practices outlined in this article, you can enhance your cybersecurity resilience, safeguard sensitive data, and ensure the continued success of your business. Cybersecurity Awareness Month is an excellent reminder for us all, but cybersecurity is an ongoing process that requires vigilance, adaptability, and continuous learning. Stay informed, stay prepared, and stay secure!





